Bitcoin’s Blockchain revolutionized the way transactions are recorded. Technology such as this never existed with a permanent ledger, decentralized and timestamps to prove the chain of evidence and proof of digital confidence mechanism to make it a perfect choice as evidence of persistent data. However, the use of Bitcoin’s blockchain for user data as evidence is not easy, because Nakamoto’s Bitcoin technology creation has a center of gravity as the “currency” of the transaction, rather than saving the attachment data. This article describes the data as evidence used for blockchain and compares several new solutions.
Bitcoin’s blockchain data as proof of evidence
Bitcoin’s most famous of the data as evidence that Genesis should block Merkle Root embedded information: “The Times 03 / Jan /This entry corresponding to the message is created Bitcoin day (2009/01/03) British newspaper The Times headline news headlines.
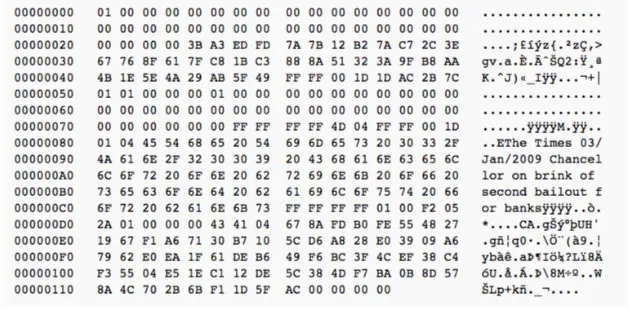
But Merkle Root’s data as evidence method is not suitable for other purposes, since the latter part of the tile generation is generated, and the random data can not be used in accordance with the Merkle algorithm. In the early development of Bitcoin, many people used fake Bitcoin addresses for storing in blockchain transactions and receiving encoded data, but most of these applications were only used to demonstrate the feasibility of the technology, rather than practicality. The use of fake bitcoin receiving address was not only inconvenient, but also restricted the number of words, and all transferred to a false address Bitcoin that was going to be permanently lost.
Perhaps in order to prevent any further expansion of the false transactions, Bitcoin core from the 0.9 version began offering an OP_RETURN transaction code specifically for storing user data. While the use of Bitcoin Foundation’s OP_RETURN in this document does not represent Bitcoin blockchain to be recognized as a distributed data storage, however, the use of OP_RETURN to store information on Blockchain transactions as evidence everywhere. With the complete system as evidence, the blockchain can be perfectly applied to electronic evidence, intellectual property, copyright registration, authentication, marriage registration, land registration, traceability of food products and other fields.
The first site to provide proof of the existence as a service ProofOfExistence.com. Users spend about $5 on the site that can be used for any group of characters, or file hash value to be stored within OP_RETURN Bitcoin transaction value. For example the following blockchain transaction and the hash data is ebb8f3b9828e2dc82b180958e0f1e6f8ecbc2f948d2ee16740ad2f0e0c6874f3
saved:
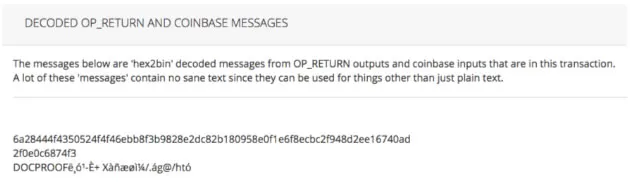
in this case, OP_RETURN first eight characters of “DOCPROOF” is a signature Proof Of Existence site.
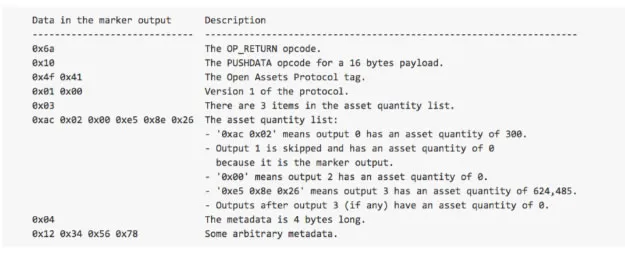
OP_RETURN can also be used by “color credits” (Colored Coin) techniques, such as the famous Open Assets protocol. “Colored coin” technology is used for tracing some of the ins and outs of a particular bit of money, this can be used to distinguish these particular types of currencies on Bitcoin Blockchain and has been termed color. They have some special properties, such as support for proxy or rallying point, which has nothing to do with the value of the bit denomination. Color coins can be used as an alternative currency, commodity certificates, intellectual property and other financial instruments, such as stocks and bonds. OP_RETURN Open Assets underlying technology using tracking color assignments for each coin. The following is an example of the transaction:
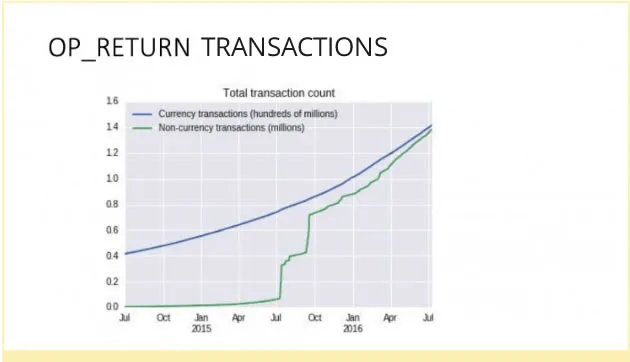
After 2015, the use of the relevant transaction OP_RETURN region continued to rise, indicating that large-scale development of this technology is being utilized.
However, the maximum limit of OP_RETURN is that every transaction is allowed to save only 40 bytes of data. For most of the data as evidence applications, this is not enough. This limitation has forced the majority of applications only as evidence of the relationship between key user data, or file hash. For application examples in the real estate registration, we can only use real estate registration number as evidence in Bitcoin blockchain, but not all real estate transaction data, including information on the new and old head of household, such information often is saved in the traditional system of registration in the database. This is not 100% but the timestamp blockchain brings a proven chain of evidence, proof digital secrets, and other advantages.
Square blockchain Ethernet data as evidence
Ethernet data storage blockchain Square Syndrome bits credits many similarities, it is also stored in the common data link in an Ethernet Square. In this specific implementation, in addition to the use of similar transactions with Bitcoin additional records outside, Ethernet Square blockchain can create a new contract to store user data.
Private chain/chain data as evidence
In 2014, the Western financial industry began a strong interest in core bitcoin blockchain technology. At the center of the blockchain technology, financial contracts can be built to help them intelligently resolve cross-border remittances, equity allocation, stocks, futures, derivatives trading, and greatly reduce transaction costs and to establish centers of credit. However, in order for Bitcoin’s blockchain to be the representative, the public chain was in a state of complete freedom of disorder at the center, which has unacceptable risks in the financial industry. The common chain for user data as evidence has limitations of technology. In such an environment, private chains and alliances sprung up like a chain up rapid development. Large investment banks and financial institutions have begun to develop their own private chains. Including Bank of America, Deutsche Bank, Citibank, Fidelity, Nasdaq and so on.
In order to coordinate the promotion of blockchain technology and application development, various alliances were formed in the blockchain industry alliance. For example, R3 blockchain alliance the US banking industry, China also has Chinaledger and Gold Chain Alliance, and the best white label exchange provider participates in such initiatives.
Compared to the public and private chain, alliance chain has its unique advantages:
-
- A controlled and orderly “decentralized.” Because enterprise or alliance entirely owned a private chain/chain alliance, the situation such as being stolen by hackers tampering with the data will not occur. Similarly, Ethernet Square DAO theft of funds does not occur in the private chain/chain alliance. Even relatively safe Bitcoin also will face 51% ownership of attack, which is a totally unacceptable risk in the formal financial sector.
- Ultra-fast transaction speed. Bitcoin and other public chains perform 10 transactions per second, once every ten minutes certified technical bottlenecks in the private chain can easily break several hundred times the level of transaction throughput.
- Transaction costs are equal or close to zero. Each transaction in the public bitcoin chain etc. is required to pay fees to the “miners”. In a private chain/chain alliance, such a transaction fee is essentially zero.
- To improve privacy protection, data is stored in the internal or business alliances, unrelated third parties and alliances with the private chain data are completely inaccessible to achieve maximum privacy protection.
- Complete freedom and free data as evidence. This could also be the largest private chain advantage chain and alliances. Because the private chain and chain alliance can customize the data structure blocks and transaction records, without compromising the entire network data storage capacity and speed of response, the system can be a complete record of the user’s data file to blockchain and permanent preservation and forensics.
It is worth mentioning that the super books project (Hyperledger project) IBM and the Linux Foundation also developed a protocol private enterprise chain.
It is foreseeable that, just as the Internet and corporate intranets from initial rejection to peaceful coexistence. The public and private chain can not be replaced because of their respective advantages will be based on different scenarios and mutually dependent.
Cross-chain data as evidence
“The use of public and private chains as cross-chain technology can have the advantages of both chains.”
VitalikEthernet Square founder
private chain and chain-League does not mean that people will reduce the use of public chains. The obvious advantage of the public chain, a fully transparent public book brings credibility. Credibility is one of the conditions necessary for permanent data as evidence, but the public did not like the private chain as easy and low-cost data as evidence. Is there a technology that can be integrated simultaneously with private and public chains and having respective advantages of each of them?
“Cross-chain” technology that came into being under such demand. Cross-link technology is the key to realize the value of the network, it is the private chain of private chains and chain alliance separate from the dispersion in the intranet to the public and to expand the chain bridge connection.
Factom (through notary) is one of the early adopters of the “cross-link” technology, the Canadian start-up company has been successful at raising more than $700 million. Factom created a distributed, autonomous agreement, client-defined record chain (Chains of Entries) data as evidence, and then by the security mechanism is based on an anchor blockchain (Records) will be registered in the records as evidence Bitcoin public accounts.
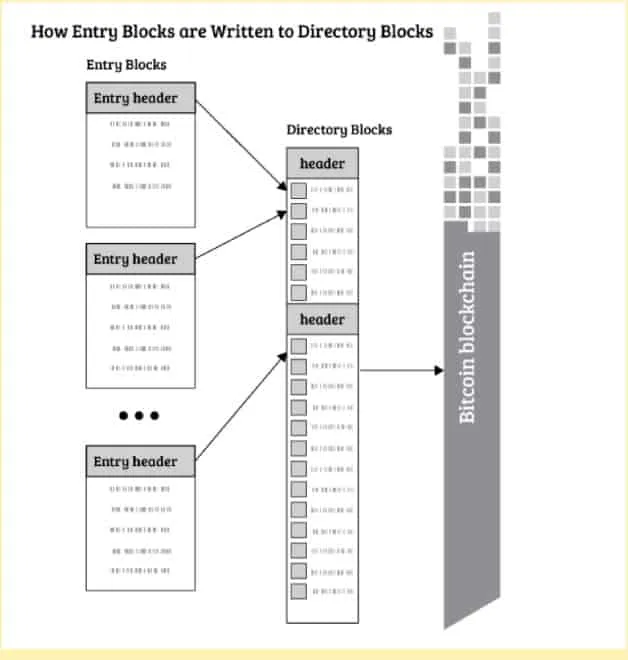
In the figure above, Factor uses its private chain architecture for user data as evidence. The algorithm then uses the private anchoring chain grafted book blocks to a common currency in the book bit.
The specific process of the anchoring algorithm is as follow, this algorithm uses OP_RETURN before the introduction. Because the corpus of user data already registered in the private chain anchoring Lieha Xi hash algorithm needs only to register the value recorded in the private bit chain block currency transactions, so protocol to meet the 40-bit bytes of credit limits. The anchored algorithm ensures the integrity of data in the private chain because any tampering with the data will trigger changes to the code containing the hash value encryption and digital time stamp immediately. The bit in common currency trading book anchoring linkage timestamp, and the hash value of private users credibility chains required.
References
- “Bitcoin: A Peer-to
- “Evidence of Absence.” Wikipedia
- “Block Timestamp.”
- “OP_RETURN and the Future of Bitcoin
- “On Public and Private Blockchains.
- “Fatcom Whitepaper.”
- “Hyperledger Whitepaper.”