Key Takeaways
- The HealthBridge PoC proves a fully role-isolated, real-time clinical patient portal can be built and validated in six weeks.
- Database-level Row-Level Security in Supabase removes PHI exposure risk structurally – not by relying on application-layer checks.
- React Native and Supabase deliver sub-2-second performance and zero crashes across iOS and Android from a single shared codebase.
- Zero double bookings under concurrent load is a structural outcome from database-layer transaction locking, not performance luck.
- We are not HIPAA-certified. Every system we build has HIPAA guidelines embedded into the architecture from the first line written.
- A focused PoC is not a shortcut. It is the most responsible first step before committing a full budget to an untested concept.
A patient opens your app at 11 PM, anxious about a lab result they have been waiting on all day.
They log in, find the document, and exhale. No phone call tomorrow morning. No uncertainty about who saw their data or where it went.
That moment of relief is what a well-built patient portal actually delivers. Most healthcare organizations across America are not delivering it.
The gap between what patients expect from digital health tools and what clinical software actually provides has never been wider. Patients manage their finances, track their health, and run their lives through apps that never go down. Then they try to reschedule a follow-up with their doctor and wait on hold for twelve minutes.
That frustration is not just a UX problem. It is a revenue problem. It is a retention problem. And in healthcare, it is a trust problem that compounds quietly until patients stop showing up.
That is exactly why we set out to Build a HIPAA-Ready Patient Portal with React Native and Supabase – and prove it could be done right, in six weeks, without cutting a single corner on security.
Why Most Patient Portal Builds Fail Before They Go Live
There is a dangerous assumption circulating across many healthtech teams: that building on a reputable modern stack automatically makes an application ready for regulated healthcare data.
It does not.
Most platforms do not provide full regulatory protection out of the box. Relying on a third-party backend to handle Protected Health Information without a custom-engineered security layer is the digital equivalent of building a state-of-the-art clinic and leaving patient files open on the reception desk.
That gap is exactly what this PoC was built to close.
We built the HealthBridge Patient Portal, a HIPAA-ready mobile proof of concept using React Native and Supabase, in six weeks. This breakdown covers how it came together, what we validated, and what it means for healthcare organizations planning a custom patient portal.
According to ONC’s 2024 data brief, app-based access to patient records jumped from 38% in 2020 to 57% in 2024. Mobile-first patient engagement is not a future trend. It has already arrived.
What a Real Patient Portal Needs to Do – and Why Most Healthcare Teams Get It Wrong
At its core, a patient portal is a secure digital platform that connects patients to their provider outside of an in-person visit. It handles scheduling, messaging, records access, and document delivery – all without routing a single interaction through the front desk.
Most organizations treat it like a convenience feature. A box to check. A login page bolted onto their EHR vendor’s system.
That approach is exactly why so many portals fail to move the metrics that actually matter: call volume, no-show rates, patient retention, and staff productivity.
A modern, production-grade patient portal has to accomplish three things simultaneously – and it has to do all three without compromise.
Access control at every layer: Patients only see their own data. Doctors only manage their assigned patients. Administrators have system-wide oversight without touching clinical records outside their scope. Role separation cannot live at the UI level – it must be structural, enforced at the database before any data is ever returned.
Clinical workflow fidelity: A portal that cannot handle real-time scheduling conflicts, timezone-aware booking, or secure document delivery is not a clinical tool. It is a web form with a login screen. Real workflows demand real engineering.
Compliance by design: Adhering strictly to HIPAA regulations is not something you layer onto a finished application. It is something you engineer from the first line of database schema. Signed expiring URLs for PHI files, privacy-first push notifications, immutable audit trails – these are architecture decisions, not post-launch patches.
Why US Healthcare Organizations Should Build Instead of Buy
Most US healthcare organizations default to vendor software because it feels like the faster, safer path. In the short term, it sometimes is. The long-term math rarely works out in the organization’s favor.
The vendor lock-in problem: Legacy portals charge per-provider licensing fees that scale against you as your practice grows. You pay indefinitely. You never own the intellectual property. When the vendor deprecates a feature your staff depends on, your only option is to adapt or pay for an upgrade you did not ask for.
A custom build inverts that equation entirely. The investment is front-loaded. The returns compound over time as licensing fees disappear, workflows sharpen, and the technology scales with your organization.
McKinsey’s 2024 analysis of digital health systems found that approximately 70% of health system executives expect the highest impact from digital front door investments – platforms that let patients manage their care online rather than through phone calls and paperwork.
The patient experience gap: Vendor portals deliver identical experiences to every organization that buys them. Your patients get the same interface as the clinic across town. A custom portal is built around your patients, your workflows, and your brand. The experience is defined by your product decisions, not a software company’s default settings.
The ownership advantage. A custom-built portal is intellectual property your organization controls outright. You decide what gets built next. You decide how data is handled. As patient expectations shift across United States healthcare markets, you move with them – on your terms, not a vendor’s roadmap.
| Factor | Vendor Portal | Custom-Built Portal |
| Recurring Cost | Per-provider licensing, ongoing | No per-seat fee |
| IP Ownership | Vendor retains all rights | You own it outright |
| Workflow Control | Vendor defines the product | Your clinical team defines it |
| Customization | Rigid, template-constrained | Built to your exact workflows |
| Scalability Cost | Grows with provider headcount | Fixed infrastructure cost |
| Competitive Edge | Identical to every other buyer | Built for your patients and brand |
| Payback Path | No payback – perpetual obligation | Realized as licensing fees are eliminated |
Why React Native and Supabase Are the Right Stack for Secure Healthcare App Development
Choosing the right technology stack for a clinical application is not a preference question. It is a compliance question, a performance question, and a long-term scalability question – all at once.
By pairing React Native with Supabase, we bridge the gap between a standard mobile application and a high-performance, security-first healthcare mobile app that can hold up under real clinical and regulatory scrutiny.
React Native as the application layer.
React Native manages the interface and data flow across both iOS and Android from a single shared codebase. Its component-based architecture is ideal for modular clinical tools where every feature – the booking engine, the records library, the notification system – operates independently but stays in perfect sync.
We paired it with Zustand for lightweight global state management. When a doctor updates their schedule, the calendar view updates instantly – no heavy Redux overhead, no unnecessary re-renders consuming performance headroom.
TypeScript in strict mode eliminates entire classes of runtime errors at the compiler level. In a regulated environment, catching malformed data structures before they reach production is not a nice-to-have. It is a clinical safety requirement.
The modular architecture also means growth does not require rebuilding. Telemedicine integrations, AI-assisted scheduling, wearable data inputs – each can be added without touching what already works.
Supabase as the security-first backend.
Standard BaaS platforms are built for general-purpose applications. Supabase was chosen specifically because it delivers the combination of database-level security, row-level access enforcement, and encrypted file storage that regulated health data demands.
PostgreSQL Row-Level Security means every query is mathematically validated by the database engine before a single row of data is returned. Role enforcement is structural – it does not depend on a developer remembering the right check on every route.
Signed, expiring URLs ensure PHI files are never permanently exposed via a public link. Supabase’s Team and Enterprise tiers support execution of a formal Business Associate Agreement – the legal foundation required for full HIPAA compliance in any production healthcare environment.
Together, these two technologies produce a system that does not just look like a healthcare application. It behaves like one, with the security guarantees and performance benchmarks that clinical use actually demands.
Inside the HealthBridge Patient Portal: A Look at the Real Build
The HealthBridge PoC is a modular clinical platform built on React Native 0.81.5 with Expo SDK 54 and Supabase as the secure backend.
This is not a simple UI with a login screen. Every screen, every interaction, and every data boundary was engineered to meet real clinical and compliance demands from the ground up.
Most healthcare mobile applications fall into one of two failure categories. Either they are built fast with consumer-grade tooling and collapse under compliance scrutiny – or they are built slowly by enterprise vendors and fail on performance and usability.
HealthBridge was built to sidestep both failure modes entirely.
The engineering brief was clear: validate that a focused, senior-led team could produce a HIPAA-ready, role-isolated, real-time clinical system inside a six-week window – without compromising on security, and without sacrificing the performance benchmarks patients expect from modern applications.
Every architectural decision maps to that brief. Nothing in the system exists for demonstration purposes. Every feature directly validates a workflow that a real clinical environment demands in production.
What the System Was Built to Validate
Before the first line of code was written, we defined the specific questions the PoC needed to answer with real evidence – not assumptions.
Can database-level RLS handle complex role logic at clinical scale? The answer needed to come from production-equivalent load testing, not a theoretical architecture review.
Can a React Native application deliver sub-2-second performance across all critical workflows on both iOS and Android simultaneously? Consumer-grade performance in a regulated, role-isolated system is a harder engineering problem than it appears from the outside.
Can push notifications surface timely clinical alerts without ever exposing Protected Health Information on a device lock screen? This is a compliance requirement most teams treat as an afterthought – and then cannot retrofit cleanly onto a finished system.
Can secure document delivery be built in a way that leaves no permanent PHI exposure window under any mobile network condition? The answer had to hold under real network interruption testing, not just stable Wi-Fi in an office environment.
Every feature in the HealthBridge build exists to answer one of those questions with a validated, measurable result.
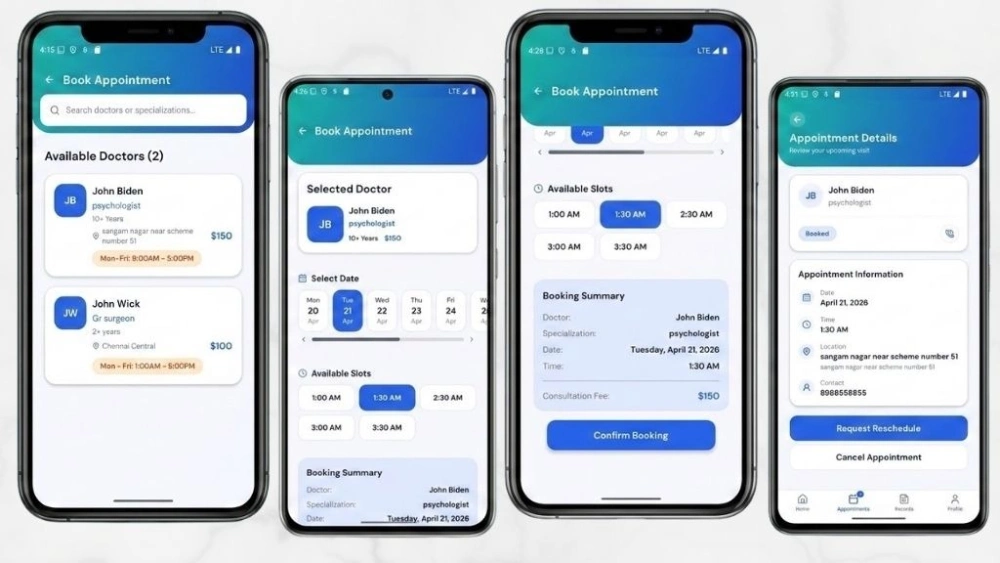
Key Features Built Into the System
The PoC was designed to close the gap between generic mobile applications and professional-grade clinical software. Every feature present directly validates a core healthcare workflow.
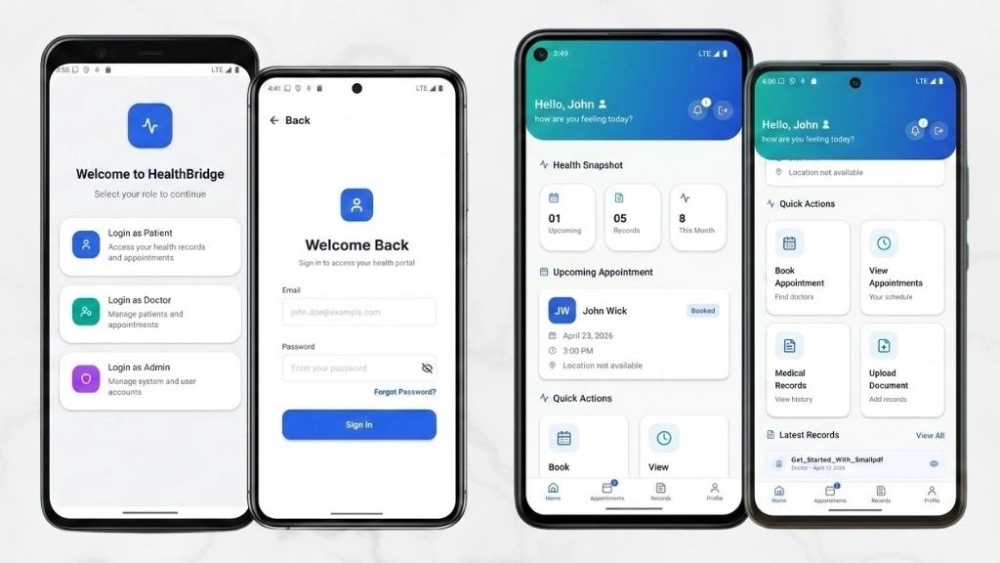
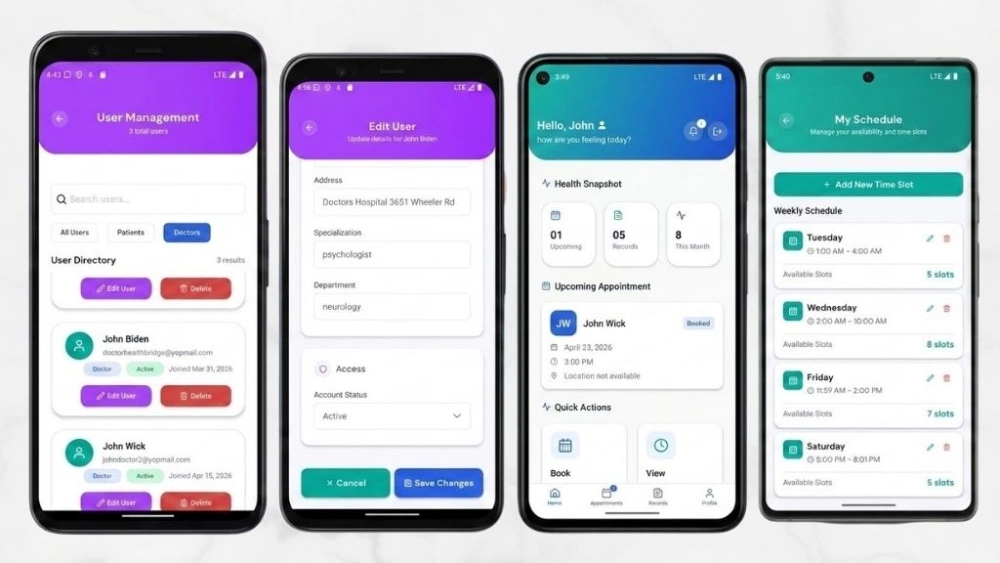
Role-Based Navigation Isolation
Three completely separate navigation trees for patients, doctors, and administrators. The separation is structural, not visual. A doctor’s session cannot navigate into the patient booking flow. A patient’s session cannot reach the admin dashboard.
The isolation is not achieved by hiding menu items or running permission checks at the component level. It is enforced at the navigation stack itself – the code for one user environment is never loaded into the session of another.
This approach eliminates an entire category of security vulnerabilities before they can be introduced. There is no route a developer could accidentally leave open. Unauthorized navigation is architecturally impossible – not just visually concealed.
Real-Time Schedule Availability Engine
A deterministic booking engine that calculates doctor availability by comparing working hours against existing appointments and buffer requirements, resolved to the minute.
The engine does not estimate or approximate. It queries current schedule state, applies buffer window rules, and returns only genuinely available slots before the user ever attempts to submit a booking request.
During concurrent load testing that simulated peak clinic hours – multiple patients attempting to book the same provider simultaneously – the system recorded zero double bookings. That outcome is not a performance achievement. It is a structural one. Database-layer transaction locking makes a double booking mathematically impossible, not just statistically unlikely.
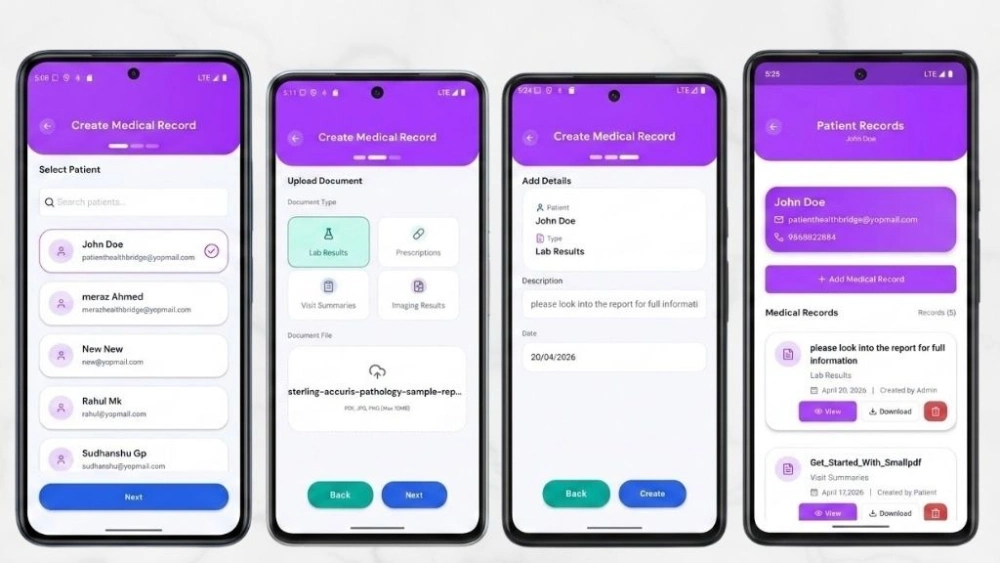
Secure Medical Document Delivery
Lab results, intake forms, and imaging reports are delivered via signed URLs that expire after a defined time window. PHI is never accessible through a permanent public link under any circumstance.
When an administrator uploads a document, the file goes directly into Supabase Storage under controlled access. The patient receives a privacy-first notification. When they tap through to view the file, a temporary secure token is generated on demand, fetches the document, and delivers it directly.
The moment that session ends, the access window closes. There is no persistent URL that could be forwarded, screenshot-linked, or cached at an intermediate server. Every access event is logged. The exposure window is controlled, time-limited, and fully auditable at every step.
Privacy-First Push Notifications
Every notification is engineered to exclude Protected Health Information from the device lock screen. The alert surfaces a secure message prompt – never a diagnostic detail, a test result name, or a provider note.
Standard push notification implementations display message content directly on the lock screen. In a healthcare context, a patient receiving a lab result notification while their phone is visible to a family member or coworker creates immediate, uncontrolled PHI exposure.
HealthBridge notifications eliminate that risk by design. The patient knows a message is waiting. They retrieve the content only after authenticating inside the application. Timeliness and privacy are preserved simultaneously – without any tradeoff between the two.
Soft-Delete Audit Trails
No record is ever permanently erased. Every administrative action toggles an active flag rather than deleting a row, maintaining the immutable audit trail that healthcare compliance demands at every level.
Healthcare compliance does not only require protecting data in the present. It requires the ability to reconstruct the complete history of every administrative action that touched clinical data – going back as far as the record exists.
A hard delete is an audit gap. A soft delete with a timestamp and actor ID is a compliance record. Every deactivation, every document removal, and every scheduling change in HealthBridge creates a log entry that cannot be overwritten, altered, or purged by any user in the system.
The Architecture: Role-Isolated from the Ground Up
The application enforces strict separation of concerns across three distinct layers. Each functions as a defense-in-depth control point – meaning that even if one layer were somehow bypassed, the next would still enforce the correct access boundary independently.
The database layer: PostgreSQL Row-Level Security policies inside Supabase act as the primary defense. Every query is evaluated by the database engine before data is returned, regardless of what the frontend requests. Even a deliberately broad query cannot retrieve records that the authenticated session is not authorized to access.
The navigation layer: React Navigation 6 isolates the three user environments into completely non-overlapping navigation trees. A patient session cannot import the doctor API service module. Each role’s environment exists in a separate code boundary. This structural separation acts as the secondary defense against any accidental data exposure at the application layer.
The state layer: Zustand manages global session state and user preferences without Redux overhead. TypeScript in strict mode enforces data integrity across every component boundary – catching mismatched data structures at compile time, before they ever run in a clinical environment.
How a Transaction Actually Flows
When a patient attempts to book a 2:00 PM appointment slot, this is the exact sequence the system executes:
- The booking engine checks availability against working hours and existing appointments, resolved to the minute.
- The Supabase client sends the booking request to the backend.
- PostgreSQL evaluates the Row-Level Security policy, confirming the session token matches the required access scope before any write executes.
- Zustand captures the confirmed booking and triggers the privacy-first confirmation notification.
Security enforcement is a database-layer guarantee on every single transaction – not an application-layer assumption that depends on a developer remembering to add the right check on every rout
Also Read: Patient Portal Mobile Application Development with React Native & Expo
How Each Feature Solves the Compliance-Speed Tradeoff in Healthcare Software Development
The assumption that speed of delivery and regulatory compliance are mutually exclusive is one of the most expensive beliefs in healthcare technology. The HealthBridge build challenges that assumption with evidence.
Role-based authentication: The system identifies the user’s role at login and routes them into a strictly isolated navigation stack immediately. When a doctor logs in, the patient booking flow is not hidden from view – it is structurally absent from their navigation tree entirely. That hard separation eliminates an entire category of security bugs before a developer ever has the chance to introduce them.
Real-time scheduling without conflicts: The booking engine calculates availability by comparing working hours against existing appointments and buffer times, resolved to the minute. During concurrent load testing that mirrored real peak clinic conditions, the system recorded zero double bookings. That result is architectural – not fortunate.
Secure medical document delivery: An administrator uploads a lab result. The patient receives a privacy-first notification. When they tap through, a temporary secure token fetches the document directly from Supabase Storage. The PHI file is never held at a permanent public address. Every access event is logged. The signed URL expires, leaving no persistent exposure window behind.
Privacy-first push notifications: In a healthcare context, any notification that surfaces clinical content on a device lock screen creates uncontrolled PHI exposure. Every HealthBridge notification excludes Protected Health Information entirely. Patients receive timely alerts. Their privacy holds even when their phone is visible to others.
System Feedback and Visual States
In a clinical environment, ambiguous system states destroy trust faster than almost any other UX failure. The application keeps every user fully informed throughout every interaction.
| System State | What the User Sees |
| Booking Processing | Real-time availability confirmation before submission |
| Document Uploading | Upload progress indicator with clean error recovery on network drop |
| Notification Delivery | Confirmation badge update without PHI on the lock screen |
| Admin Action Logged | Soft-delete confirmation with audit trail entry timestamp |
| Error State | Specific, actionable error messages – never silent failures |
The Four Hardest Technical Challenges We Solved
According to the HHS HIPAA Security Rule, regulated entities must implement technical safeguards that protect against unauthorized access to electronic Protected Health Information. Here is exactly how we honored that requirement in architecture – not just in policy documentation.
Challenge 1: Row-Level Security for Complex Clinical Role Relationships
The problem: Healthcare data is deeply interconnected. A doctor must see records for their assigned patients and only those patients. Writing SQL policies that handle many-to-many role relationships without triggering infinite recursion or degrading query performance is a genuinely difficult engineering problem that most teams underestimate.
The solution: We designed an optimized schema using junction tables and built strictly non-recursive RLS policies around them. Secure database functions with elevated privileges handle role relationship verification independently, keeping query execution fast while maintaining absolute data isolation between every role in the system.
Challenge 2: Timezone-Aware Scheduling Across a Distributed Patient Population
The problem: Patients and providers operating across different timezones – a reality in any telemedicine context – create booking conflicts and calculation errors when local times are stored directly in the database. A 2:00 PM slot in California is a 5:00 PM slot in New York. Storing either local value breaks the booking engine’s arithmetic.
The solution: We enforced a strict UTC-only policy at both the database and API levels. Timezone conversion happens exclusively at the rendering layer, in the View component. The booking engine operates in a completely timezone-neutral environment – making availability calculation mathematically correct regardless of where the patient or provider is located.
Challenge 3: Document Upload Reliability on Real Mobile Networks
The problem: Uploading large PDF files over a mobile connection is consistently prone to interruption. A standard API call that times out mid-upload leaves the system in an ambiguous state and the user with no actionable information about what happened or what to do next.
The solution: We integrated Expo’s native file system tools with Supabase Storage APIs and implemented chunked uploads with robust, specific error recovery logic. When a network connection drops mid-upload, the user receives a clear, actionable alert. No silent failures. No spinner that never resolves. No system state left ambiguous.
Challenge 4: Type Safety Across Complex Navigation Boundaries
The problem: Passing complex data objects between mobile screens without enforced type definitions creates runtime bugs that only surface under edge cases – typically in production, under real clinical conditions, when the cost of failure is at its highest.
The solution: We defined global TypeScript interfaces for every navigation route parameter and every API response shape across the entire application. The TypeScript compiler flags any mismatched data structure before the code ever runs. Type-related crashes were eliminated from the build entirely, not managed reactively.
| Technical Challenge | Engineering Solution | Clinical Benefit |
| Complex RLS Relationships | Junction tables with non-recursive policies | Absolute data isolation between all roles |
| Timezone Conflicts | UTC-only storage with rendering-layer conversion | Mathematically correct scheduling across all geographies |
| Upload Interruption | Chunked uploads with clean error recovery | No ambiguous states or silent data loss |
| Type Drift Across Screens | Global TypeScript interfaces for all route params | Zero type-related crashes in production |
The Validation Results: What Six Weeks of Real Testing Actually Proved
These are not projections, estimates, or vendor promises. They are results from physical device testing conducted across iOS and Android throughout the full six-week build cycle.
Zero double bookings under concurrent load: The deterministic booking engine, combined with database-level transaction locking, makes this outcome structurally impossible rather than statistically managed. A double booking in a medical setting is not a software inconvenience – it is a patient safety event with real consequences.
Sub-2-second performance across every critical workflow: Clinical staff abandon slow tools as readily as consumers abandon slow apps. A portal login that takes 6 seconds is a portal that stops being used within the first week of deployment. Every performance benchmark was met without exception.
Zero application crashes across the full test cycle: Across both iOS and Android, through six weeks of development and physical device testing that included heavy navigation patterns and concurrent document operations, the application recorded zero crashes. TypeScript strict mode and Expo’s stable native API wrappers were central to that outcome.
A foundation built for production, not for demonstration: The organization validating this PoC is not buying a throwaway prototype. They are validating a foundation that extends directly into production – with automated testing, BAA execution, and EHR integrations added on top of proven architecture.
| Performance Metric | Validated Result |
| Login and session restoration | Under 2 seconds |
| Doctor availability calculation | Under 1 second |
| Appointment booking confirmation | Under 2 seconds |
| Rendering 50 complex medical records | Under 1.5 seconds |
| Downloading a 2MB PDF on standard mobile connection | 3 to 5 seconds |
| Double bookings during concurrent load testing | Zero |
| Application crashes across full test cycle | Zero |
| Mobile memory during heavy navigation | Under 150MB |
Build vs. Buy: The Analysis Every Healthcare Decision-Maker Actually Needs
The hidden cost of a vendor portal is not the number on the licensing invoice.
It is the compounding cost of rigid workflows that force clinical staff to work around software rather than with it. It is the productivity lost to clunky patient interfaces that push call volume up instead of down. It is the dependency on a vendor roadmap that may never reflect what your organization actually needs from its technology.
A custom patient portal app development engagement requires a focused upfront investment. In return, it eliminates the perpetual licensing obligation, delivers a product built specifically around your clinical workflows, and produces owned intellectual property that scales with your organization without triggering additional cost at every growth milestone.
Research compiled by HIMSS on patient portal initiatives consistently shows that portal adoption, active logins, secure messages, and lab views all improve significantly when the tool is well-designed and actively promoted to patients. A portal that patients actually use is the only one that delivers measurable ROI.
The build vs. buy answer, at its core, comes down to one word: control. Control over the patient experience, the product roadmap, the data architecture, and the long-term cost structure of your digital health infrastructure.
Why Choose Bitcot for Healthcare Software Development
Building a healthcare technology product that is fast, secure, genuinely compliant, and actually useful to clinical staff sits at the intersection of regulatory knowledge, architectural discipline, and deep understanding of the workflows that make a medical practice function day to day.
As this PoC demonstrates clearly, the difference between a portal patients abandon after their first session and one that becomes a genuine operational asset lies entirely in the decisions made before a single screen is designed.
We do not just build healthcare software. We engineer clinical infrastructure. Every decision we make maps directly to a compliance requirement, a measurable business outcome, or a patient experience standard the organization actually has to meet – not a standard that sounds good in a pitch deck.
Compliance architecture from day one: We build Row-Level Security into the database schema from the start, not onto the finished application as a second pass. Audit trails are immutable by design. PHI handling is enforced at the infrastructure layer – not managed by application-layer rules that a developer has to remember to apply on every route.
Senior-only engineering teams: Every architect, developer, and product lead on a healthcare engagement is senior level. No junior engineers learning their craft on your regulated system and your patient data.
Domain depth across real clinical workflows: We understand the operational difference between a scheduling conflict and a patient safety event. Our architecture reflects that clinical understanding throughout – not just the technical requirements document.
Long-term partnership model: We do not deliver a PoC and move on to the next engagement. We carry the architecture through production, support post-launch iterations, and function as a strategic technology partner as the organization’s digital needs evolve over time.
Proven React Native and Supabase expertise: We have already solved the hardest problems in this stack – Row-Level Security for complex role relationships, timezone-aware scheduling, chunked document upload recovery, type-safe navigation boundaries. Organizations do not pay us to figure out what we already know how to do.
The PoC Advantage: Why This Is the Most Responsible First Step in Healthcare Technology
One of the most valuable aspects of our approach is that a PoC with us is never a throwaway exercise.
Because we engineer the core architecture correctly from the start – the security model, the role isolation logic, the booking engine, the document delivery system – the production build extends what works rather than rebuilding from scratch on a tighter timeline.
Accelerated timelines: Validating architecture and clinical workflows in a focused six-week engagement compresses the risk out of the production build phase. Organizations enter production investment with demonstrated evidence, not unvalidated assumptions.
Reduced operational risk: A validated PoC proves the stack before a large-scale budget is committed. Executives and clinical leaders make investment decisions based on real performance metrics from real device testing – not projected outcomes from vendor presentations.
Tailored clinical workflows: The foundational architecture is proven. The specific features, EHR integrations, and patient-facing experience are built entirely around the organization’s unique clinical workflows and patient population.
Whether you are running a busy multi-location specialty clinic, a hospital system evaluating a modern alternative to your legacy EHR vendor portal, or a digital health startup preparing to validate your first clinical product concept – the conversation starts in the same place: a focused Proof of Concept that validates the approach before you scale it into production.
Explore our case study to see how our mobile application development capabilities translate into production-ready healthcare solutions in real-world use.
Final Thoughts
Building a healthcare application is not purely a technical challenge. It never has been.
For patients, it is about feeling safe enough to book an appointment, retrieve a lab result, or receive a sensitive notification without wondering who else can see that information.
For clinicians, it is about having a digital environment that genuinely supports their work rather than adding friction and compliance uncertainty to an already demanding clinical day.
For founders and product teams building across America, it is about finding the responsible path between moving fast and building something that holds up under real regulatory and operational scrutiny – not just in a controlled demo environment.
What the HealthBridge project proves is that you do not have to choose between a modern user experience and a compliant one – or between speed of delivery and genuine depth of security.
With the right architecture – security enforced at the database layer, role isolation built into the navigation structure from day one, PHI handled through expiring access rather than permanent exposure – React Native and Supabase can be the foundation of a patient portal that scales confidently into production without needing to be rearchitected six months after launch.
When security, data isolation, and audit integrity are designed in from the start, they stop being constraints. They become the reason the product is trusted by everyone who depends on it.
We work with hospitals, specialty clinics, therapy practices, and digital health startups across the United States to build patient-facing infrastructure aligned with real clinical and regulatory needs – not theoretical checklists.
Whether you are validating a first concept, modernizing a portal patients have outgrown, or rethinking how your practice handles scheduling and document delivery entirely – talk to our team. We will tell you exactly what a Proof of Concept would validate for your workflows and what the path to production actually looks like.
Frequently Asked Questions (FAQs)
What is a patient portal and what should it actually do for a medical practice?
A patient portal is a secure digital platform that connects patients to their healthcare provider outside of in-person visits. A well-built portal manages scheduling, medical records access, document delivery, and appointment reminders – all without routing interactions through the front desk. For the practice, it automates routine patient communication, measurably reduces front desk call volume, and drives improvements in appointment adherence and long-term patient retention. For patients, it delivers the on-demand access they already expect from every other digital service they use.
How do you build a HIPAA-ready patient portal the right way?
Start at the database layer, not the application layer. Implement PostgreSQL Row-Level Security so every data query is validated by the database engine before any information is returned to the frontend. Use signed, expiring URLs for all protected health information file delivery. Design push notifications to exclude sensitive health details from device lock screens. Build soft-delete audit trails into the data model from the start. In production, execute a business associate agreement with your backend infrastructure provider and commission a third-party penetration test before any public-facing launch.
Is Supabase a suitable backend for healthcare applications?
Yes – when configured with the right security architecture. Supabase’s Team and Enterprise tiers support execution of a Business Associate Agreement. Developers must implement Row-Level Security policies correctly and configure Storage with proper controlled access settings. When built correctly, Supabase delivers enterprise-grade authentication, role-based data isolation, and encrypted file handling that aligns with HIPAA-guided development requirements for production healthcare systems.
React Native or native iOS and Android for a healthcare mobile app - which is the better choice?
For the overwhelming majority of patient portal use cases, React Native is the right choice. It delivers consistent sub-2-second performance across both iOS and Android from a single shared codebase, handles complex clinical workflows effectively, and eliminates the overhead of maintaining two entirely separate native builds. Native development provides a meaningful technical advantage only for applications with unusually heavy native hardware dependencies or extremely complex platform-specific UI requirements – scenarios that rarely apply to patient portal development.
How do patient portals improve operational efficiency in therapy practices and private clinics?
Through three direct, measurable mechanisms. Self-service scheduling removes routine appointment management from the front desk call queue entirely. Research published in the NIH journal found that patient portal users experienced a 53% relative reduction in missed appointments compared to non-users. Automated, privacy-first appointment reminders reduce no-show rates without adding staff workload. And digital document delivery eliminates fax handling and manual file management from the administrative workflow completely.
How do you ensure patient data security in a patient portal?
Security is achieved through multiple layers, including role-based access control, database-level security policies, encrypted data storage, secure document delivery, and audit logs. Sensitive data should never be exposed through public links or unsecured notifications.
How long does it take to build a patient portal using React Native and Supabase?
A functional patient portal can be built in a few weeks for validation purposes, depending on scope and complexity. A production-ready system may take longer due to compliance requirements, integrations, and testing.